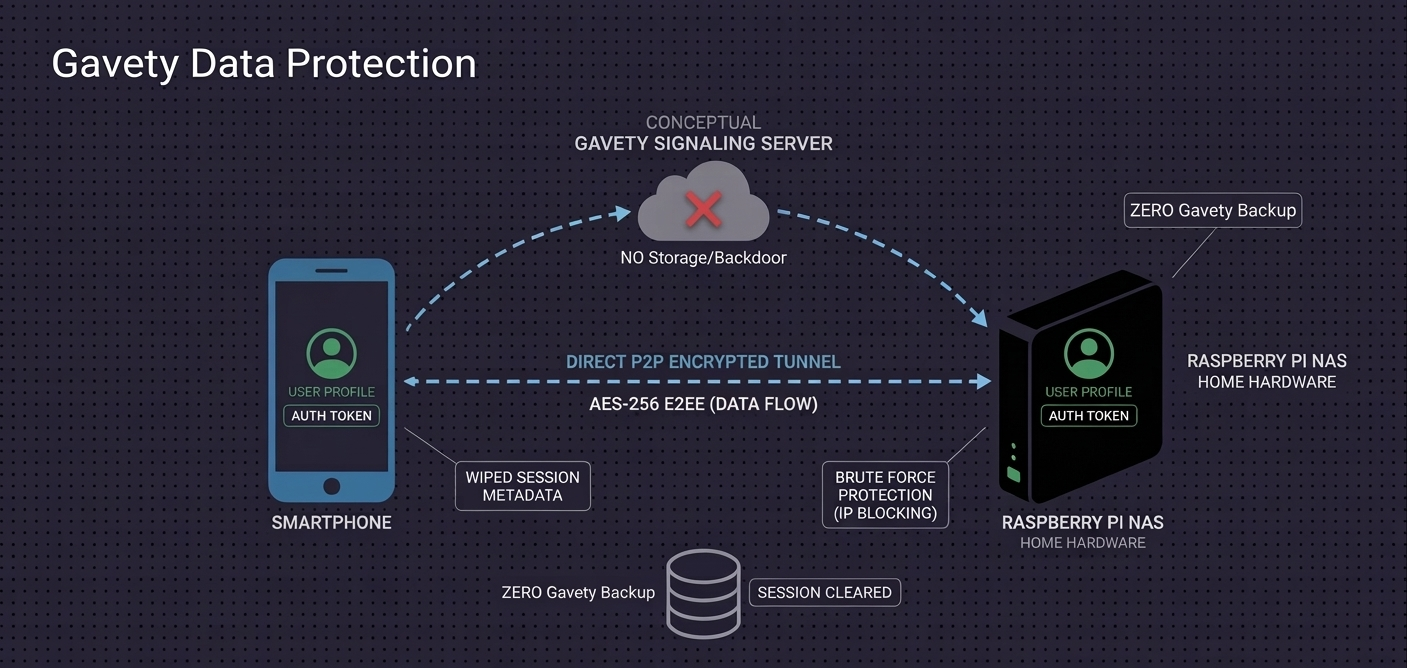
Your privacy is hard-wired, not promised
Traditional data protection relies on a company promising not to look at your files. Gavety relies on mathematics.
By using peer-to-peer tunneling, we eliminate the middleman entirely. Your flat annual fee funds continuous security auditing and the handshake infrastructure that keeps these tunnels iron-clad. Learn more about how the P2P connection works or get started with setup.